The new USB Rubber Ducky poses even greater danger
A new version of the hacking tool was released to coincide with the Def Con hacking conference this year, and its creator Darren Kitchen explained it to The Verge. New features make the latest edition more dangerous than ever, according to some tests we conducted.
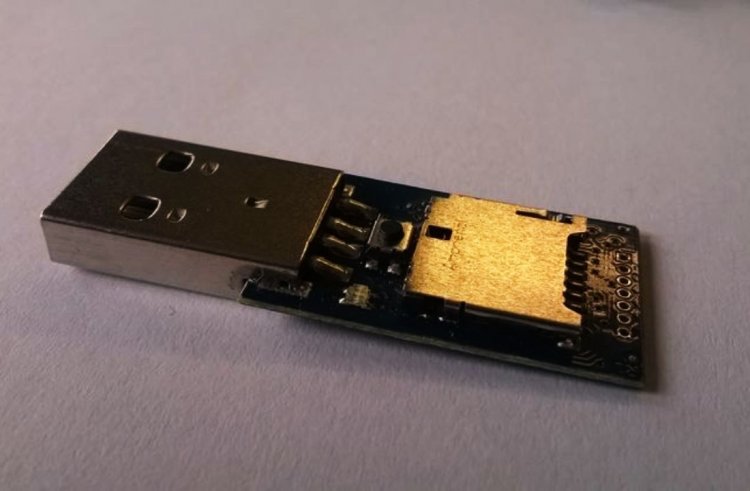
As far as the human eye is concerned, the USB Rubber Ducky looks like any other USB flash drive. It works just like a USB keyboard on a computer, which accepts keystroke commands from the device just like you would type them.

Rubber Ducky is a fan favorite among hackers and has been around for more than ten years. The latest Rubber Ducky takes a big step forward with enhanced features that make it more flexible and powerful than ever before.
The Rubber Ducky previously let users harvest login credentials by creating fake Windows pop-up boxes or by causing Chrome to send all saved passwords to an attacker's server. Despite this, these attacks had to be carefully crafted for specific operating systems and software versions, and they were not flexible enough to work across a wide range of operating systems and software versions.
To overcome these limitations, the Rubber Ducky has been updated. The DuckyScript programming language, which creates the commands the Rubber Ducky will enter into a target machine, has been upgraded. As opposed to previous versions of DuckyScript, version 3.0 offers a more feature-rich language that allows users to write functions, store variables, and use logic flow controls.
As a result, for instance, the new Ducky can check whether it is connected to a Windows or Mac machine and conditionally execute the appropriate code if it has been connected to the wrong one. A variation in the delay between keystrokes can be added by generating pseudorandom numbers.
The most impressive feature is the ability to steal data from a target machine by encoding it in binary format and transmitting it through the signals sent to the keyboard when the CapsLock or NumLock LEDs should light up.
This method would allow an attacker to take all the passwords saved on the USB drive, tell someone that the drive may be broken, and then take it back. It could be big, but most people aren't at risk since they need physical access to their devices.

A new Rubber Ducky was Kitchen's company's most in-demand product at Def Con, and 500 units were sold out on the first day. It is safe to say that hundreds of hackers already have one, and demand will likely continue for some time to come.
It also features an online development suite for creating attack payloads and compiling them, then loading them to the device. In addition, there is a "payload hub" section of the site where hackers can share what they’ve created, as well as a Hak5 Discord that provides tutorials and conversation.
A bunch of them scattered in your favorite cafe would be rare unless it's known as a hangout place for sensitive targets for $59.99 per unit. Think twice before plugging in a USB device you found lying out in public...If you do not have any experience writing or debugging code, there are a few things that can trip you up.
The Ducky had trouble entering the F4 key on a Mac for a while, but I solved the issue by sending it a different Apple keyboard device ID after I made it identify itself.
The Ducky then automatically launched Chrome, opened a new browser window, navigated to The Verge's homepage, then quickly closed it - all without the laptop user's input. The app could be easily modified to do something more nefarious than browsing technology news for a few hours of testing.









